Web Application Penetration Testing
Infopercept is a global leader in web application penetration testing; finding bugs in a number of programming languages and environments. Our security specialists have helped protect data all over the world, from webapps in highly scalable AWS environments to legacy apps in conventional infrastructure.

Vulnerability Assessment Penetration Testing Services
Network protection – and network penetration testing by extension – is changing as rapidly as the infrastructure on which it is designed. For penetration testing services that go beyond a basic vulnerability detector, you need industry experts.
Mobile App Penetration Testing
Today, both business and public organisations are using mobile apps in new and compelling ways, from banking applications to healthcare platforms. Managing security risks is a growing challenge on these platforms, with new vulnerabilities being identified on a daily basis. Is your mobile app safe from attackers?
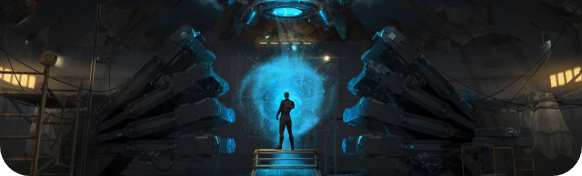
Red Team Engagements
Red Team Engagements are extremely focused evaluations that attempt to exploit sensitive data properties in the network by exploiting the vast reach that an external intruder may have had. Unlike the conventional penetration test, where our security experts are attempting to identify and exploit some potential vulnerabilities in a given scope—such as a web application—these commitments mimic a real cyber assault on the company.

Source Code Review Services
Each programming language has its own unique properties. Python is built for readability, Java is "write-one-run-everywhere" and C programmes must handle their own memory management. Similarly, each language has security features that must be considered during a comprehensive analysis of the source code.
Email Phishing Assessment
Phishing seeks to extract personal information or access from the end person by coercive communications. This type of interaction is especially efficient, since attackers will also exploit public information to generate convincing emails while impersonating somebody trustworthy—maybe even individuals inside the target company.
Vishing Assessment Services
Vishing – or Voice Phishing – is a social engineering assessment that relies on calling on target audiences to acquire or access classified information. With a more intimate approach over the phone, this individual attack vector is much more successful than phishing, it is the counterpart of an email. . . Employees who need to interact with the public, such as bank tellers and support desk workers, may be especially at risk.
Cloud Penetration Service
Penetration monitoring on the AWS cloud is special, with its own range of security requirements. Although certain flaws are mitigated by Amazon's protection policies, many businesses are vulnerable to the complexities of these services. One of the best aspects of AWS is the tremendous versatility offered to users in setting up the environment. Although versatility is a wonderful thing to have, it is also a major security issue.




