Your technologies must be continuously monitored, tuned and updated to maintain their health and availability. Infopercept's Technology Optimization Center (TOC) takes on this task for you with experts who can support leading third-party products in existing environments and new deployments.
Protect Your Investments
SAMPLE - Organization's Security Concerns
50+ Days
OS Patches Pending

75+ Days
Network Patches pending

100+ Days
Cloud Gaps not Addressed

Endless Days of Application
Gaps Pending

365+ Days
No DR Drills

200+ Days
OT / IOT Risk not Addressed

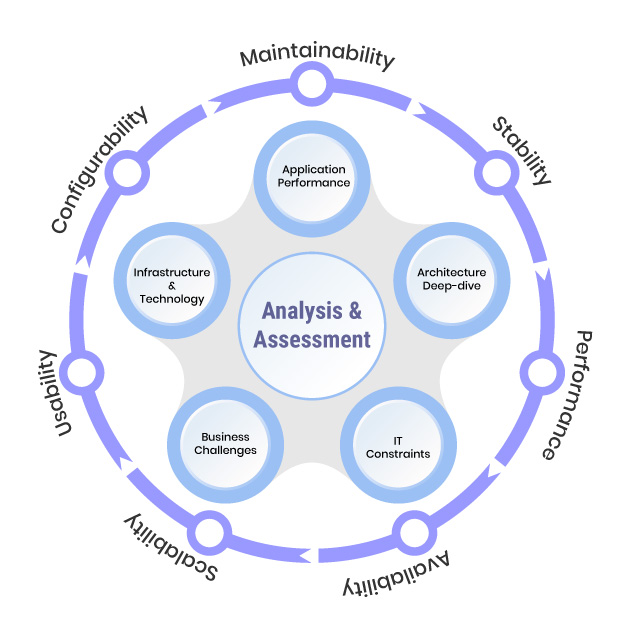
Simplified Infopercept TOC Service Process
It takes weeks for an organization to address security concerns such as Operating Systems Patching, Networks Patching, Addressing the Cloud Gaps, unavailability of DR Drills, Unaddressed OT/IOT risks, and many more. To address these business needs, organizations can take steps to simplify and optimize their IT environments: rationalize and align application portfolios, refresh platforms, deploy solutions, optimize workloads and implement intelligent automation.
Infopercept's Technology Optimization Services is done with a group of optimization experts who join hands with the clients, to provide better configuration & optimize the existing security solutions installed by the business. Our Technology Optimization Service is your one stop solution to efficiently optimize & fine-tune the existing solutions and rev them up to ensure and achieve full utilization and efficiency in terms of Cybersecurity Defense of your organization. The Technology or the Brand name has not been a concern for our experts, since we have hands-on experience across multiple technologies in the market.
Enterprises are seeking ways to lower costs and achieve greater agility, security. and resiliency. In the absence of Complex or No Security architecture with skill gaps in IT Management, the CIOs/CISOs are finding it difficult to justify the IT budget for their management, whilst having to work with multiple vendors and technologies. On the other hand with multiple vendors being involved, the organizations find it challenging to effectively manage the vendors. Companies are unable to realize the challenges regarding technologies from the vendors and majority of the time New Technology integrations are missing.
Infopercept's Technology Optimization Services
We take the approach of Continuous Security-Continuous Optimization: Security-in-and-as-Code, where we coherently support our clients to optimize the following areas
- Integrated Risk Management (IRM)
- Asset Security
- Network Security
- Identity and Access Management (IAM)
- Cloud Security
- OT / IOT Security
- Application Security
- Infrastructure Security
- Business Continuity

The Technology or the Brand name has not been a concern for our experts, since we have hands-on experience across multiple technologies in the market. In order to address challenges such as Complex or No Security Architecture, to support CISOs to justify the IT Budget, to ensure effective vendor management, and to ensure integration of new technologies is done properly; Infopercept follows the following phases
Phase 1
Environment Understanding
Today's business environments are going through several major transformations. Most business environments are increasingly dependent upon vast amounts of information. Infopercept's IT professionals spend a lot of time to thoroughly understand an organization's IT landscape. In doing so, they will be able to identify the gaps and the areas of improvement.

Phase 2
Integration, Optimization, Patch Management Across Landscape
The IT environments that support businesses are evolving from a simple machine and automation-centric operational model to a complex people and interactive service-centric operational model. Upon thoroughly understanding the organization's IT Landscape, Infopercept's IT Professionals will be implementing the best practices to integrate, optimize and manage the Patches across the landscape.

Phase 3
Ongoing Enhancements
Upon completion of the phase 02, Infopercept's IT Professionals will continue to follow the Plan-Do-Check-Act (PDCA) cycle to ensure that the organization's IT Landscape is continuously enhanced. The organizations will benefit from this exercise since there would be a better ROI from the investments made on the technologies; and Infopercept's IT Professionals vast industry experience will help bridge the skill gap for your organization.

Technology Optimization Services come with a variety of default features and functionalities; all of which are included in our standard Managed Security Services offering.
Understanding The Environment
At least one in four organizations have faced a security breach in the past 12 months, while 23 percent aren't sure if they have been breached or not. The consequences of a cyber attack on a company can be costly in a number of ways. In addition to the heavy financial cost the breach itself may pose, reputational risks, and potential litigation can also threaten a company's bottom line.
One of the main reasons is because organizations aren't fully aware of their IT Business Landscape due to various technologies being implemented, change of IT department personnel, and many such concerns.
With Infopercept's Technology Optimization Center, organizations will now be able to thoroughly understand their IT Business Landscape environment. With the Infopercept Experts assessing your organization; we will be collecting inventory across the environment, conducting configuration reviews, and proposing the best industry practices to be implemented.

Automated Patching Across Landscape with Additional Tools
Network vulnerabilities are due to the technological weaknesses that allow attackers to compromise a product and the information it holds. This process needs to be performed continuously in order to keep up with new systems being added to networks, changes that are made to systems, and the discovery of new vulnerabilities over time. Vulnerabilities on the organization's landscape increase due to the Pending Patches and Gaps not being addressed. These patches are often necessary to correct errors (also referred to as "vulnerabilities" or "bugs") in the software. Common areas that will need patches include operating systems, applications, and embedded systems (like network equipment). When a vulnerability is found after the release of a piece of software, a patch can be used to fix it. Doing so helps ensure that assets in your environment are not susceptible to exploitation.
With Infopercept's Technology Optimization Center organizations will now be able to effectively address their vulnerabilities. They will be addressed by ensuring effective patch management with system hardening, deploying tools required for automated patching, and deploying basic Cybersecurity Tools.
BENEFITS THAT INFOPERCEPT BRINGS TO ORGANIZATIONS

Security
Effective Patch management will fix vulnerabilities on your organization's software and applications that are susceptible to cyber-attacks, helping you reduce its security risk.
System Uptime
Patch management will ensure your organization's software and applications are kept up-to-date and run smoothly, supporting system uptime.
Compliance
With the continued rise in cyber-attacks, organizations are often required by regulatory bodies to maintain a certain level of compliance. Patch management is necessary to adhere to compliance standards.
Feature Improvements
Patch management can go beyond software bug fixes to also include feature / functionality updates. Patches can be critical to ensuring that you have the latest and greatest that a product has to offer.
Get Better ROI from Existing Investment
Organizations invest in People, Processes, and Technologies expecting higher Return on Investments in the running of their business operations. There are several reasons why IT investments can fail; but there are also solutions for these. At the end of the day, you and your team control the implementation. You can orchestrate the process and course-correct the implementation when you need to.
With Infopercept's Technology Optimization Center organizations will now be able to:
- Plan well, be proactive, and pull off smooth implementations,
- Present Product Integration / fine tuning possibility, to get better ROI from existing investments,
- Continuous Enhancement, Integration, and Optimization
- Deep Dive Health Checkups (Ongoing).
Conducting deep dive IT health checks on the business's systems will test how well protected your systems are and how vulnerable they might be to someone trying to get in, whether inadvertently or with serious intent.
The health checks will include testing of your External systems which links the outside world (web servers, email servers, firewalls and antivirus, internet services, VPNs and other remote access solutions as well as third party suppliers who have access to your systems); and Internal systems and infrastructure (the build and configuration of your networks, servers, applications and desktops, and internal gateways and patching at all levels).
Infopercept's IT Health Check will help organizations to identify vulnerabilities and potential problems - in your individual systems as well as your setup as a whole. It will also confirm your existing security methods as effective, so you can be confident that you are doing everything you can to protect your business. At the same time it improves the cyber awareness within your company by raising staff awareness of how important it is to follow simple best practices as one of the most underrated benefits of an IT health check. More importantly, it protects against possible future losses of productivity and downtime caused by your systems going down because of threats which could have been easily prevented.
Infopercept will help your organization to have responses to queries such as;
- Where weaknesses have been identified?
- What can or should be done about the vulnerabilities found?
- Whether best practices are being followed or not?
- Whether processes that have been set up are being followed or not?
- What are the action plans for the future?

 CASE STUDY
CASE STUDY SAMPLE REPORT
SAMPLE REPORT





